Blue Team Labs Online - Wargames
SCENARIO
A privileged USER working as local admin on a "REALLY SECURE System" opened a HOWTO for the "TIC TAC TOE" Strategy Game. Unfortunately he downloaded the HOWTO from a repository controlled by an adversary named TRUDY. We suspect exploitation was performed on the system and that persistence has been achieved. After the user noticed his system was acting strange he disconnected it from the network and the local IR unit was able to acquire a memory dump using the “dumpit” tool. You have your disposal an updated version of the VOLATILITY 3 FRAMEWORK and linux cli to perform your analysis
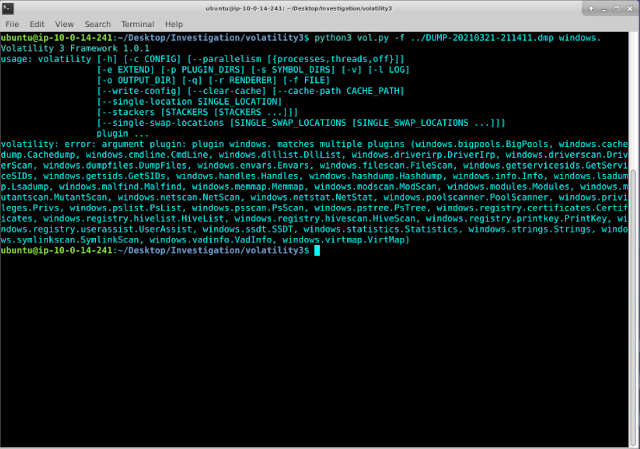
To view available windows plugins for volatility3 the following command may be used:
python3 vol.py -f ../DUMP-20210321-211411.dmp windows.
What was the System Time at time of Image Acquisition? (5 points)
python3 vol.py -f ../DUMP-20210321-211411.dmp windows.info.Info
The output shows the system time of image acquisition to be 2021-03-21 21:14:13
What's the Virtual Memory Address of the SYSTEM, SOFTWARE, and SAM Registry Hive? (5 points)
python3 vol.py -f ../DUMP-20210321-211411.dmp windows.registry.hivelist.HiveList
SYSTEM: 0xd6044824a000
SOFTWARE: 0xd60448c77000
SAM: 0xd6044b8ec000
What's the VICTIM System Name? (5 points)
RESOURCE: https://www.aldeid.com/wiki/Volatility/Retrieve-hostname
python3 vol.py -f ../DUMP-20210321-211411.dmp windows.registry.printkey.PrintKey -h
The SYSTEM hive offset is at 0xd6044824a000
python3 vol.py -f ../DUMP-20210321-211411.dmp windows.registry.printkey.PrintKey --offset 0xd6044824a000 --key 'ControlSet001\Control\ComputerName\ComputerName'
We see the victim system name is 'WOPR'
What's the VICTIM System Timezone? (5 points)
RESOURCE: https://social.technet.microsoft.com/Forums/en-US/24391355-1ebf-468a-a1a8-8b74ad794f76/time-zone-registry-key
python3 vol.py -f ../DUMP-20210321-211411.dmp windows.registry.printkey.PrintKey --offset 0xd6044824a000 --key "ControlSet001\Control\TimeZoneInformation"
The system timezone is 'GMT Standard Time'
What's the VICTIM Username, Relative Identifier (RID) and NT hash? (5 points)
We can use windows.hashdump.Hashdump to find information about the victim user.
python3 vol.py -f ../DUMP-20210321-211411.dmp windows.hashdump.Hashdump
victim username: Falken
victim RID: 1001
victim hash: b6c6f2547ed88bd3c99f6c33d3774103
What's the VICTIM Password? (Check the NT hash on crackstation.net!) (5 points)
crackstation.net found Falken's NT hash to be 'Joshua'
The system was exploited via the malicious file "TicTacToeHOWTO.doc". What's the file MD5 hash after being collected from memory? (In case you find multiple occurrences of such file in memory, consider the one on the LOWEST memory offset) (10 points)
python3 vol.py -f ../DUMP-20210321-211411.dmp windows.filescan.FileScan | grep TicTac
The virtual address of 'TicTacToeHOWTO.doc' is 0xc0843829e660
We can use windows.dumpfiles.DumpFiles to extract the file.
python3 vol.py -f ./DUMP-20210321-211411.dmp windows.dumpfiles.DumpFiles --virtaddr 0xc0843829e660
This extracts 2 files, we are interested in the file with the extension '.vacb'
The MD5 hash of TicTacToeHOWTO.doc is 3ae96eaf8a4906265dd686ca74e08c7f
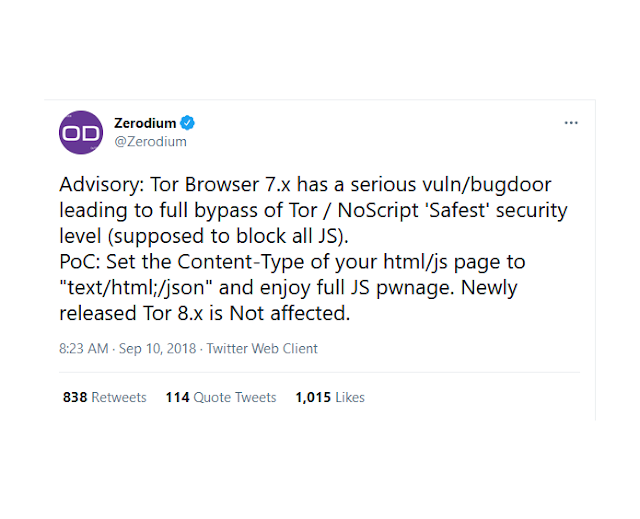
Check the previous question's hash on VirusTotal. What was the vulnerability exploited by TRUDY? (5 points)
virustotal.com finds the CVE of the exploited vulnerability to be 'CVE-2017-11882'
We know that the exploit relied on a HTML Application (HTA). What's the full path of the downloaded .hta file on the operating system? (5 points)
We reuse the windows.filescan.FileScan plugin, but this time we look for files with 'hta'.
The full path of the downloaded .hta file is
'\Users\Falken\AppData\Local\Microsoft\Windows\INetCache\IE\9IDW1R72\tictactoe[1].hta'
After exploiting the system and escalating privileges, TRUDY migrated the meterpreter shell to a SYSTEM owned process. Which process has meterpreter successfully been migrated to? (10 points)
RESOURCE: https://www.forensicfocus.com/articles/finding-metasploits-meterpreter-traces-with-memory-forensics/
python3 vol.py -f ../DUMP-20210321-211411.dmp windows.malfind.Malfind
The meterpreter process was migrated to vmtoolsd.exe with PID of 2984
We know that the VICTIM had Notepad open on his computer with a highly confidential file open. We suspect TRUDY was after this file. What's was the filename and the notepad.exe PID? (10 points)
We can use windows.cmdline.CmdLine to see what file Falken opened with notepad.exe
python3 vol.py -f ../DUMP-20210321-211411.dmp windows.cmdline.CmdLine
The highly confidential file is named secret.txt
The notepad.exe PID is 828
What's the secret message inside the highly confidential file? We know this to be something present on the previously identified process memory, starting on VAD base address of 0xc0843941db80 and with exactly 53 characters. (Hint: dump the process memory and apply "strings -n 53" to filter out the garbage) (10 points)
python3 vol.py -f ../DUMP-20210321-211411.dmp windows.vadinfo.VadInfo --help
python3 vol.py -f ../DUMP-20210321-211411.dmp windows.vadinfo.VadInfo --pid 828 --dump
This dumps pid 828 to a large number of files in the current directory
'strings -n 53 pid.828.*' returns the following output
In this output we see the message 'A strange game. The only winning move is not to play!'
TRUDY deployed an additional binary on the system. The binary was launched and had the Parent PID (PPID) of 1632 and has a strange random name. What's the md5sum of the suspicious child process when you dump its particular PID from memory? (10 points)
python3 vol.py -f ../DUMP-20210321-211411.dmp windows.psscan.PsScan --help
The PsScan help page shows that it can be used to extract process memory when given a pid.
python vol.py -f ../DUMP-20210321-211411.dmp windows.psscan.PsScan | grep 1632
Using grep to search for processes with PID or PPID of 1632 reveals a process with a filename of TSDBjNHH.exe. This file's pid is 1564, its ppid is 1632.
python3 vol.py -f ../DUMP-20210321-211411.dmp windows.psscan.PsScan --pid 1564 --dump
The process memory of pid 1564 has been dumped to a file named pid.1564.0x400000.dmp
The MD5 hash of the process is 2a61b1d9ba01cee97c21ba706b08fec5
This process tries to connect to an external IP Address. What's the C2 backup IP address used by this adversary? (10 points)
The plugin windows.netscan.NetScan can be used to find connections made by the victim host
python3 vol.py -f ../DUMP-20210321-211411.dmp windows.netscan.NetScan
This reveals a connection initiated by pid 1564 and filename TSDBjNHH.exe to the ip address
195.201.24.87 with an unusual destination port number of 8443





















Comments
Post a Comment